Helow,
in this post i would like to share about connecting to vmware esxi server using mac address. As dedfault, VMware only give us vmware esxi client for windows platform.
how about the user using mac? actually there are a solution provided by vmware, it is by using vsphere web client. The problems occur for me is, I just switching from window to Mac and have not yet install web client support in esxi server.
For you that has same problem, you can try to follow below step for connecting to esxi server using mac.
1. download vmware fusion, it is free
2. install vmware fusion
3. from vmare fusion, choose File ==> connect to server
4. input your server ip address, username and password
5. you can start managing the host from server library
Happy virtualizing All!!!
Let's Share...
the more you Share, the more you Get
Senin, 14 November 2016
Selasa, 26 Juli 2016
warm-up-post - I have a new name
hohohoho, it is very long time not posting in this blog. the latest post was almost two years ago. actually this blog is intended to post what I have learned in college but not from class. But because im no longer in the college (actually still, currenly im taking my master in business management, but i cant do all i want to do like in my bachelor degree L) I will be posting everything i think need to remember.
the other reason to start posting again is because i just gave this blog new name (www.herdi.id) ,but still you can access the old uri on http://for-shares.blogspot.co.id/. hahaha :D
Ok, enough for this warm-up-post, i will be posting another post very soon.
see ya..
the other reason to start posting again is because i just gave this blog new name (www.herdi.id) ,but still you can access the old uri on http://for-shares.blogspot.co.id/. hahaha :D
Ok, enough for this warm-up-post, i will be posting another post very soon.
see ya..
Minggu, 12 Januari 2014
Load Balancing Using Httpd2.4 with tomcat instance as Web Server
Load balancing is a computer networking method for distributing workloads across multiple computing resources, such as computers, a computer cluster, network links, central processing units or disk drives. Load balancing aims to optimize resource use, maximize throughput, minimize response time, and avoid overload of any one of the resources. Using multiple components with load balancing instead of a single component may increase reliability through redundancy.
Here is the load balancing scenario in my lab,
- Apache httpd 2.4 will be use as load Balancer
- Apache Tomcat 1 will be use as web server 1
- Apache Tomcat 2 will be use as web server 2
Setting up httpd2.4 as load balancer
Before beginning we have to download the Httpd2.4 that we will use as load balancer. You can download it here.
--> extract it in the specific directory
After that, we will need a connector (mod_jk.so) so Apache httpd2.4 can connect to tomcat instance. You can download it here.
--> copy it to [Apache Installation dir]\modules\ mod_jk.so
The next step is about configuring "httpd.conf" that located in [Apache Installation dir]\ conf\httpd.conf
--> Add this line to that file
here is the slide of my presentation in my college about Load Balancing, download it.
here is the complete project about my load balancing, download it.
Sabtu, 28 Desember 2013
Basic tips for Secure Browsing
1. Never keep same password for different services you use online like gmail , facebook, bank accounts etc.,
2. Use multiple accounts so that you dont get spams in your personal/ official email address.
3. Install good Antivirus and Two way firewall.
4. Use VPN for hiding identity and secure browsing when using internet out of your home.
5. Update your OS, Antivirus, Firewall and Browsers regularly.
6. Install a good spyware & Adware scanner .
7. Never provide personal information openly in public websites. Share your information carefully.
8. Never click on unwanted or suspiicious links. It may be hacking attempt.
9. Change your passwords regularly to increase the security of your daily actiivities.
source: https://www.facebook.com/Trickonics
2. Use multiple accounts so that you dont get spams in your personal/ official email address.
3. Install good Antivirus and Two way firewall.
4. Use VPN for hiding identity and secure browsing when using internet out of your home.
5. Update your OS, Antivirus, Firewall and Browsers regularly.
6. Install a good spyware & Adware scanner .
7. Never provide personal information openly in public websites. Share your information carefully.
8. Never click on unwanted or suspiicious links. It may be hacking attempt.
9. Change your passwords regularly to increase the security of your daily actiivities.
source: https://www.facebook.com/Trickonics
Rabu, 25 Desember 2013
How to reveal saved asterisk password in the browser without any tool
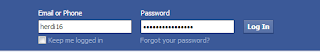
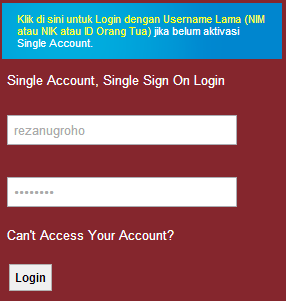
What do you want to do when you open the web browser and then find a page with saved credential like this?
Do you want to know that saved password? :D
well, here is few step to reveal that asterisk password without any tools:
1. Right click on the saved password and then choose inspect element
2. Find text "<input type='password' name='bla bla bla >"
3. Change "type='password'" to "type='text'"
4. Enter
5. Now you can reveal the asterisk password
Next question, how to avoid this happening?
to avoid this happening you can do this things,
1. If there are anyone else that can use your computer, never save your password when your browser ask you to save the password.
2. if you really the one that can use your computer don't forget to lock your computer when you leave it. The simplest way if you can Windows OS you can press (Windows + L) to lock your computer.
-Your awareness is your computer security key- :)
Do you want to know that saved password? :D
well, here is few step to reveal that asterisk password without any tools:
1. Right click on the saved password and then choose inspect element
2. Find text "<input type='password' name='bla bla bla >"
3. Change "type='password'" to "type='text'"
4. Enter
5. Now you can reveal the asterisk password
Next question, how to avoid this happening?
to avoid this happening you can do this things,
1. If there are anyone else that can use your computer, never save your password when your browser ask you to save the password.
2. if you really the one that can use your computer don't forget to lock your computer when you leave it. The simplest way if you can Windows OS you can press (Windows + L) to lock your computer.
-Your awareness is your computer security key- :)
How to know the real extension of a file?
In computer forensic challenge we usually work with a file with no extension like the file in red rectangle below
The next question, how we can know the real extension of those files?
If you want to know the real extension of those files the first thing you can do is check the "file signature" from those files.
what is file signature?
2 - 4 bytes = 4-8 hex
to know the "file signature" a file the first thing you can do is check the hex value of that file (because most of file signature is stored as hex value on database),
to do this you can follow this steps:
1. download this tool "HxD Editor"
http://www.softpedia.com/get/Programming/File-Editors/HxD.shtml
2. after download, just install and open it.
3. open the file you want to know the real extension (click menu File --> Open)
4. copy first 4-8 hex value from HxD Editor
in example we copy first 6 digit Hex value : FF D8 FF
5. find file signature database in internet, like this one
http://en.wikipedia.org/wiki/List_of_file_signatures
the other file signature database:
http://www.garykessler.net/library/file_sigs.html
http://www.filesignatures.net
6. rename the file with real extension
ta daaaa :)
For your exercise please find the right extesion for "Mocca" file :D
this is the file that you can download.
The next question, how we can know the real extension of those files?
If you want to know the real extension of those files the first thing you can do is check the "file signature" from those files.
what is file signature?
a file signature is data used to identify or verify the content of a file. In particular, it may refer to:
- File magic number: bytes within a file used to identify the format of the file; generally a short sequence of bytes (most are 2-4 bytes long) placed at the beginning of the file (wikipedia)
2 - 4 bytes = 4-8 hex
to know the "file signature" a file the first thing you can do is check the hex value of that file (because most of file signature is stored as hex value on database),
to do this you can follow this steps:
1. download this tool "HxD Editor"
http://www.softpedia.com/get/Programming/File-Editors/HxD.shtml
2. after download, just install and open it.
3. open the file you want to know the real extension (click menu File --> Open)
4. copy first 4-8 hex value from HxD Editor
in example we copy first 6 digit Hex value : FF D8 FF
5. find file signature database in internet, like this one
http://en.wikipedia.org/wiki/List_of_file_signatures
the other file signature database:
http://www.garykessler.net/library/file_sigs.html
http://www.filesignatures.net
6. rename the file with real extension
ta daaaa :)
For your exercise please find the right extesion for "Mocca" file :D
this is the file that you can download.
Jumat, 27 September 2013
Tahapan Instalasi Active Directory pada Windows Server 2008 R2
Active Directory adalah layanan
directory yang terdapat pada system
operasi server. Active Directory terdiri
atas basis data dan juga layanan directory. Active
Directory menyediakan sarana untuk mengelola identitas dan hubungan yang
membentuk organisasi. Active Directory yang
ada pada Windows Server 2008 R2 menyediakan berbagai fungsi untuk melakukan
konfigurasi yaitu: administarasi system,
pengguna (user), group, computer, dan pencarian directori. Active Directory juga memberikan cara untuk mengelola credential untuk mengizinkan pengguna yang sah
yang dapat mengakses baik itu perangkat aplikasi maupun data.
Untuk lebih lengkapnya silakan download paper berikut ini :
Langganan:
Postingan (Atom)